Cisco Crypto Key Generate Rsa Ssh 2
SSH (Secure Shell) is a secure method for remote access as is includes authentication and encryption. To do this, it uses a RSA public/private keypair. There are two versions: version 1 and 2. Version 2 is more secure and commonly used. Last but not least, to configure SSH. Aug 25, 2016 Switch (config)# crypto key generate rsa Enables the SSH server for local and remote authentication on the Switch and generates an RSA key pair. Generating an RSA key pair for the Switch automatically enables SSH. We recommend that a minimum modulus size of 1024 bits. When you generate RSA keys, you are prompted to enter a modulus length.
So it looks as if there is no point in the 'crypto key generate rsa' command if i follow it up with the 'crypto key generate rsa usage-keys label sshkeys mod 1024' command, i just wanted to make sure the first wasn't need for the second to work or something screwy like that.
Using an RSA Public/Private key pair instead of a password to authenticate an SSH session is popular on Linux/Unix boxes. Digital Ocean, a Virtual Private Server (VPS) provider, has this advice on how you should log into their Droplets: “you should use public key authentication instead of passwords, if at all possible. This is because SSH keys provide a more secure way of logging in compared to using a password alone. While a password can eventually be cracked with a brute-force attack, SSH keys are nearly impossible to decipher by brute force alone.” Plus, it means you never have to type C!$c0 again!
Cisco IOS now has support for using SSH with RSA keys. There are many resources showing how to configure SSH with RSA keys on the Internet and I have included several in the references section to give you more information. In this blog I am going to show how to configure a switch and create the public/private key pair using Puttygen for Windows.
OpenSSH ships with most *nix OS’s like Mac OSX and Ubuntu so you don’t need a separate program to generate the key pair. There are resources in the reference section on how to create the keys using OpenSSH. As a side note, Microsoft announced that it is going to build OpenSSH support into Powershell so you may be able to log into the next release of Windows server using SSH.
Download Puttygen
Recently there was some malware floating around using the name putty.exe. Make sure that you download putty and puttygen from http://www.chiark.greenend.org.uk/~sgtatham/putty/download.html
The MD5 check sums are at this link – checksums. On Windows you can use the official MS tool FCIV to check the MD5 sums. If you prefer a GUI Hashtab is a nice tool that integrates into the right click menu. It’s free but does require registration and an email address.
Once you have Puttygen double click to start it up. Enter a description for your key and a passphrase. I recommend storing your passphrase in a password manager so that you don’t for get it. Select SSH-2 RSA and enter 2048 for bits. Enter a comment for your key pair and click Generate. You will be asked to move the mouse around to generate some entropy.
Once the key is done you can select it and paste it into the switch. You should also save the public and private keys to a file.
Open Putty and create a session. Click on Auth under the SSH menu. Under Authentication parameters click Browse and select your private key. Click on Session and save your session.
You can also click on Data under Connection and set up an Auto-login username:
Don’t forget to save your session. If you always log in using the same settings you can set all of them and then save the session as the default session.
Setup the Cisco Device
I’m using a 3750X-48P-L running IOS Version 15.2(3)E1 for this example.
Configure a time server
While this isn’t absolutely necessary it’s the first thing I do on any production device.
3750x(config)#ntp server 129.6.15.29 prefer
3750x(config)#clock timezone PST -8 0
3750x(config)#clock summer-time PDT recurring
Configure an IP domain name, create the RSA private key and enable SSH
3750x(config)ip domain-name pu.pri
3750x(config)crypto key generate rsa modulus 2048 exportable
3750x(config)ip ssh version 2
Note the “exportable” parameter. This isn’t required but I wanted to point that out that you can make the keys exportable. It’s not so important in this case but if you have setup GetVPN on a router you absolutely want to export the keys used for the tunnels. If you don’t and the router fails you will have to touch EVERY tunnel once you replace the hardware. If you have exported the keys you just reload them on the new hardware and call it a day.
I have a link to a Cisco TAC podcast on GetVPN and DMVPN in the references that does a great job of explaining how to use RSA key pairs and why you MUST export them. If you don’t want to listen to the entire podcast jump to minute 40 or so and listen from there. I highly recommend listening to all the TAC Security podcasts.
View the key
3750x#sh crypto key mypubkey rsa
% Key pair was generated at: 22:53:25 PDT Jul 16 2015
Key name: 3750x.pu.pri
Key type: RSA KEYS
Storage Device: not specified
Usage: General Purpose Key
Key is exportable. Redundancy enabled.
Key Data:
30820122 300D0609 2A864886 F70D0101 01050003 82010F00 3082010A 02820101
00ABDBCC B2C31B8F 264A92D0 8C56D9F2 B5B2E8E3 354BDA0E A3C6F287 5D5A66D4
5BDF9E25 A866E5CA 3B6641CB 375410E9 4F142169 8334C1DC 88F8BC34 80129A62
F59E0B90 B329A728 93F96C32 EE2AF78A DFF692A0 1649D911 F8DA728B 108B2790
4954B60D 62999C52 2F832900 61A654A3 938EF6FB EB85F88F 2A3740D6 BE57B4C8
C55EE8A0 4F6A23AB 416CB6F3 9F211B2E 2640ED4E 7AB03B6F 4B982F91 4965B834
DB00254F F00E5D4D D3C102AA 75A78903 862D22AF 290D85B2 09D1D8A6 4A5D66C4
4B7A2E0F 437A4566 864130ED 82411160 4198AFC1 AC0C8946 2FE181A5 6AFBD4AF
20E8D5A5 83BA182F A5FA8352 48E55CF5 1A5C2F38 B61A57A1 DC7229F8 994C87B2
C5020301 0001

Export the key
3750x(config)#crypto key export rsa 3750x.pu.pri pem terminal 3des SecurePassPhrase
% Key name: 3750x.pu.pri
Usage: General Purpose Key
Key data:
—–BEGIN PUBLIC KEY—–
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAq9vMssMbjyZKktCMVtny
tbLo4zVL2g6jxvKHXVpm1FvfniWoZuXKO2ZByzdUEOlPFCFpgzTB3Ij4vDSAEppi
9Z4LkLMppyiT+Wwy7ir3it/2kqAWSdkR+NpyixCLJ5BJVLYNYpmcUi+DKQBhplSj
k472++uF+I8qN0DWvle0yMVe6KBPaiOrQWy2858hGy4mQO1OerA7b0uYL5FJZbg0
2wAlT/AOXU3TwQKqdaeJA4YtIq8pDYWyCdHYpkpdZsRLei4PQ3pFZoZBMO2CQRFg
QZivwawMiUYv4YGlavvUryDo1aWDuhgvpfqDUkjlXPUaXC84thpXodxyKfiZTIey
xQIDAQAB
—–END PUBLIC KEY—–
—–BEGIN RSA PRIVATE KEY—–
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,3E0EAC17DCDE45B0
Hq3gxGpuI8eE1WvPPr3Xw8bcrzV+cCHvGLu6D3atp5O89sQIQUMxI/udppUMWnbI
7iIpuFIJfTM9WfkNBvBBDVR4jjZfm8sHVqNll2flwqhwnPITaRBgJreaUaHL4xlU
xmPEkApfu7odjZS6sn93tZ1W1+Smn5XzAoBhKNi2N0oDjR0ruubUsPBEWcBFuzJQ
k5SKVsYl++DcA7WgFlL14/B6GgQTEoVJ6R9N14cOCJVORIhCYSxZlds4rNMeuX/9
RffhZriB+0OWJvEnxmgoKpshOX7hQVYpbHyPuJ2sDMwxwqv27uQPVp96kUhm33US
lA/7EEHzWnbvJI4TRCWFSLbaUAiPqA9NMalD6lGqpADqtaoPFPCq4pfQdMc1Lfm8
x0C8Yk+YhQDs/NNyem0xj1swKcxnbcisKzqvFdKNy4Oo60sZZD0dzBlQpxNGbQbo
GxqUPkf2nJ9/1cLnrYQ2gE5f3EN9vfBJbNWx4I5D4uNFaM/an2JxCatOwM7qglhh
C2kPofynBgxfedxSRwButo0VFt4wNs7Ijk2o/IlfZDpaxZoisQwz21z3gnKSTuVQ
gwBcfwXLLyP7e4xTmHcHQfpzu2XQjJmHTqYBU2c/fsBXYYmbwfKgp2UeeVgCVfWP
7Cd53PtRc6kycodB6phcHRdnBd2TDame6IP7dHKASbcuHXFmBRAPRG2wpt90BzFC
WRaRAkSvf8b2GAKjoHJF8Pw/eQBgc9JPXY5UkGapRT+fkw1fS99GUXPiI5EYMmws
BYOOMBgY7h+FCHCuuQ/FpZEyRYHBMYbUSZ0Vt4ikQh4L6kdOz5fC04IUXwtDnOh0
Lv9Un8YRS9tL4JzXjTauByhNxj+JEQnUCBXjTEbdJGZ1k8LGygfD8ixwK8StQ3pe
nwCrJwBPP5oORJmZssdTubyldZTy/abgnZMoJ9RgBI2muxL+3EtzvLnrUvaD4SkK
X8InDcEk8WlmI5joMe+wxrgKehWuRddD0iB+CfpE9N90fRGEvS/awHx2RVdh9VFo
b85l5ebRC8FsIckQPp8qc71vcrJ4P2D88FT5VshD4aUhZYWdLDRPLzbMrFOprjqu
sSU/cxL7V6w3954PzlAV0yVyiQ9TnPCSdPPBVLV8oJzXo/6LWWND72Xi9ORbCTIP
GcoSURd8oQwzmEbwuxeAv2JmZyiJCTZWOvDOc0mZCr7NgkbkZPH+wi8aJzsv9gDU
ISLBu4c+MQ5At4wad6fXLHeAOpKTNJ7nlfHgcgCichQv/tC+yZgvMiV3d6aumXri
dZLBThpuXOWNxkYO3tpZfNv1sRCfwTrn7sr/zW8mDvGMSNlwqOLwDGnH2G5HbQFm
G/w70NxwY5jQniOA/FurorBtm1P68uji7i1yHM6jctfElJXKcBWNyKHsLEc8Uk1A
2CdVPt9fXoUAqjcyV8rqyzn91P6E04ilqUp129oABcVAh7A3lr4u76Nt5Na5qDuo
zzP/2yZAi6dKQJOxpyMjQo4zkKPVPDjkJOwJtfIqGsC5glpYbMXGmUPhsYapAyK6
maXbb2L9aVDnZxl8bt0vHSBDpGVBThXX/iQgZaV0eGzSEhgwZF2wOuLTIMTnJX3C
—–END RSA PRIVATE KEY—–
Configure AAA authentication
The aaa new-model command causes the local username and password on the router to be used in the absence of other AAA statements. Once you enter “aaa new-model” you will not be able to enter “login local” on vty line configuration. If you had login local configured it will be removed.
When you create the username be sure to include a secret. I you don’t anyone will be able to login with just the username. As always, create a strong secret and use a password manager to store it.
3750x(config)#username cisco privilege 15 secret ^8(nn-!#who
3750x(config)#aaa new-model
3750x(config)#aaa authentication login default local
3750x(config)#aaa authorization exec default local
(Authentication through the line password is not possible with SSH)
Configure the line
3750x(config)#line vty 0 4
3750x(config-line)#transport input ssh
3750x(config-line)#logging sync (prevents console messages from interfering with your inputs)
Add your PUBLIC key to the device.
Open the public key file you created in puttygen. Copy the text between the comments. If you generated a 2048 bit key you will need to paste it into notepad and break it into smaller pieces or you may see “%SSH: Failed to decode the Key Value” when you exit:
3750x(config)#ip ssh pubkey-chain
3750x(conf-ssh-pubkey)#username hubbard
3750x(conf-ssh-pubkey-user)#key-string
3750x(conf-ssh-pubkey-data)#$QAAAQEAkp2EDdpi86+h2aygSIYLt6DvoeFVKYJ1S/Zr
3750x(conf-ssh-pubkey-data)#$ylIDAzWA+G9TolxvWTLzTcUR/+Ykk74mqQbuGTxpteP
3750x(conf-ssh-pubkey-data)#$IStVVjycGYHRSJv9H2C8OQYMcHCR7yM/36TTFRIjLfV
3750x(conf-ssh-pubkey-data)#$PaWM45mr8DI2/sJkwESLWWGJKYiaSxEG6h+gLA5DePj
3750x(conf-ssh-pubkey-data)#$SP4zpktK7KD51NQDy8vx3jVVhkkANGbFfz/uWk2Uhno
3750x(conf-ssh-pubkey-data)#$DQeBxtZbxEGU4tXDZmRbPGVmk8DtFh9LVRCxUTQ
3750x(conf-ssh-pubkey-data)#exit
3750x#sh run sec ssh
ip ssh version 2
ip ssh pubkey-chain
username hubbard
key-hash ssh-rsa 0C029272CF23E61C4315A0D59E565B76
transport input telnet ssh
3750x#
3750x#sh run b 0 4
line vty 0 4
transport input ssh
line vty 5 15
Note – You can use the HASH instead of the key for the next devices you setup. Instead of using “Key-string” in the ip ssh pubkey-chain statement use “key-hash ssh-rsa 0C029272CF23E61C4315A0D59E565B76”.
Login using your SSH Keys!
References
SSH RSA authentication works in IOS release 15.0M
Secure Shell Version 2 Support in IOS 15
TAC Security Podcast Episode #25 – GETVPN and DMVPN
SSH/OpenSSH/Keys – A good Ubuntu article on OpenSSH
How to create ssh keys with putty to connect to a virtual private server (VPS) – The Digital Ocean Tutorial. They have a lot of good tutorials.
Using SSH/SCP on Mac OS X in the Terminal app
Kali Linux remote SSH – How to configure openSSH server – A great tutorial.
SSH using public key authentication to IOS and big outputs – A Cisco Support Forum article. It includes a Bash script for remotely executing commands.
SSH with key authentication on Cisco IOS devices – A good blog for Windows users
How To Protect SSH with fail2ban on Ubuntu 12.04
Synchronise remote SSH authorised_keys
Contents
Introduction
Secure Shell (SSH) is a protocol which provides a secure remote access connection to network devices. Communication between the client and server is encrypted in both SSH version 1 and SSH version 2. Implement SSH version 2 when possible because it uses a more enhanced security encryption algorithm.
This document discusses how to configure and debug SSH on Cisco routers or switches that run a version of Cisco IOS® Software that supports SSH. This document contains more information on specific versions and software images.
Prerequisites
Requirements
The Cisco IOS image used must be a k9(crypto) image in order to support SSH. For example c3750e-universalk9-tar.122-35.SE5.tar is a k9 (crypto) image.
Components Used
The information in this document is based on Cisco IOS 3600 Software (C3640-IK9S-M), Release 12.2(2)T1.
SSH was introduced into these Cisco IOS platforms and images:
SSH Version 1.0 (SSH v1) server was introduced in some Cisco IOS platforms and images that start in Cisco IOS Software Release 12.0.5.S.
SSH client was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.1.3.T.
SSH terminal-line access (also known as reverse-Telnet) was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.2.2.T.
SSH Version 2.0 (SSH v2) support was introduced in some Cisco IOS platforms and images starting in Cisco IOS Software Release 12.1(19)E.
Refer to How to Configure SSH on Catalyst Switches Running CatOS for more information on SSH support in the switches.
Refer to the Software Advisor (registered customers only) for a complete list of feature sets supported in different Cisco IOS Software releases and on different platforms.
The information presented in this document was created from devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If you are in a live network, make sure that you understand the potential impact of any command before you use it.
Conventions
Refer to Cisco Technical Tips Conventions for more information on document conventions.
SSH v1 vs. SSH v2
Use the Cisco Software Advisor (registered customers only) in order to help you find the version of code with appropriate support for either SSH v1 or SSH v2.
Network Diagram
Test Authentication
Authentication Test without SSH
First test the authentication without SSH to make sure that authentication works with the router Carter before you add SSH. Authentication can be with a local username and password or with an authentication, authorization, and accounting (AAA) server that runs TACACS+ or RADIUS. (Authentication through the line password is not possible with SSH.) This example shows local authentication, which lets you Telnet into the router with username 'cisco' and password 'cisco.'
Authentication Test with SSH
In order to test authentication with SSH, you have to add to the previous statements in order to enable SSH on Carter and test SSH from the PC and UNIX stations.
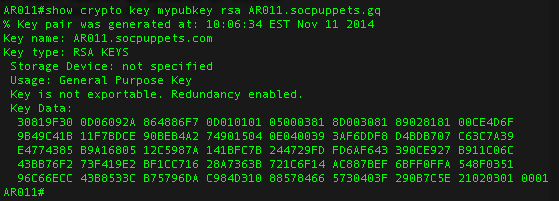
At this point, the show crypto key mypubkey rsa command must show the generated key. After you add the SSH configuration, test your ability to access the router from the PC and UNIX station. If this does not work, see the debug section of this document.
Optional Configuration Settings
Prevent Non-SSH Connections
If you want to prevent non-SSH connections, add the transport input ssh command under the lines to limit the router to SSH connections only. Straight (non-SSH) Telnets are refused.
Test to make sure that non-SSH users cannot Telnet to the router Carter.
Set Up an IOS Router or Switch as SSH Client
There are four steps required to enable SSH support on a Cisco IOS router:
Configure the hostname command.
Configure the DNS domain.
Generate the SSH key to be used.
Enable SSH transport support for the virtual type terminal (vtys).
If you want to have one device act as an SSH client to the other, you can add SSH to a second device called Reed. These devices are then in a client-server arrangement, where Carter acts as the server, and Reed acts as the client. The Cisco IOS SSH client configuration on Reed is the same as required for the SSH server configuration on Carter.
Issue this command to SSH from the Cisco IOS SSH client (Reed) to the Cisco IOS SSH server (Carter) in order to test this:
SSH v1:
SSH v2:
Setup an IOS Router as an SSH server that performs RSA based User Authentication
Complete these steps in order to configure the SSH server to perform RSA based authentication.
Specify the Host name.
Define a default domain name.
Generate RSA key pairs.
Configure SSH-RSA keys for user and server authentication.
Configure the SSH username.
Specify the RSA public key of the remote peer.
Specify the SSH key type and version. (optional)
Exit the current mode and return to privileged EXEC mode.
Note: Refer to Secure Shell Version 2 Support for more information.
Add SSH Terminal-Line Access
If you need outbound SSH terminal-line authentication, you can configure and test SSH for outbound reverse Telnets through Carter, which acts as a comm server to Philly.
If Philly is attached to Carter's port 2, then you can configure SSH to Philly through Carter from Reed with the help of this command:
SSH v1:
SSH v2:
You can use this command from Solaris:
Restrict SSH access to a subnet
You need to limit SSH connectivity to a specific subnetwork where all other SSH attempts from IPs outside the subnetwork should be dropped.
Generate Rsa Ssh Key
You can use these steps to accomplish the same:
Define an access-list that permits the traffic from that specific subnetwork.
Restrict access to the VTY line interface with an access-class.
This is an example configuration. In this example only SSH access to the 10.10.10.0 255.255.255.0 subnet is permitted, any other is denied access.
Note: The same procedure to lock down the SSH access is also applicable on switch platforms.
Configure the SSH Version
Configure SSH v1:
Configure SSH v2:
Configure SSH v1 and v2:
Note: You receive this error message when you use SSHv1:
Note: Cisco bug ID CSCsu51740 (registered customers only) is filed for this issue. Workaround is to configure SSHv2.
Variations on banner Command Output
The banner command output varies between the Telnet and different versions of SSH connections. This table illustrates how different banner command options work with various types of connections.
| Banner Command Option | Telnet | SSH v1 only | SSH v1 and v2 | SSH v2 only |
|---|---|---|---|---|
| banner login | Displayed before logging into the device. | Not displayed. | Displayed before logging into the device. | Displayed before logging into the device. |
| banner motd | Displayed before logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. |
| banner exec | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. | Displayed after logging into the device. |
Unable to Display the Login Banner
SSH version 2 supports the login banner. The login banner is displayed if the SSH client sends the username when it initiates the SSH session with the Cisco router. For example, when the Secure Shell ssh client is used, the login banner is displayed. When the PuTTY ssh client is used, the login banner is not displayed. This is because Secure Shell sends the username by default and PuTTY does not send the username by default.
The Secure Shell client needs the username to initiate the connection to the SSH enabled device. The Connect button is not enabled if you do not enter the host name and username. This screenshot shows that the login banner is displayed when Secure Shell connects to the router. Then, the login banner password prompt displays.
The PuTTY client does not require the username to initiate the SSH connection to the router. This screenshot shows that the PuTTY client connects to the router and prompts for the username and password. It does not display the login banner.
This screen shot shows that the login banner is displayed when PuTTY is configured to send the username to the router.
debug and show Commands
Before you issue the debug commands described and illustrated here, refer to Important Information on Debug Commands. Certain show commands are supported by the Output Interpreter Tool (registered customers only) , which allows you to view an analysis of show command output.
debug ip sshâDisplays debug messages for SSH.
show sshâDisplays the status of SSH server connections.
show ip sshâDisplays the version and configuration data for SSH.
Version 1 Connection and no Version 2
Version 2 Connection and no Version 1
Version 1 and Version 2 Connections
Sample Debug Output
Router Debug
Note: Some of this good debug output is wrapped to multiple lines because of spatial considerations.
Server Debug
Note: This output was captured on a Solaris machine.
What can go Wrong
These sections have sample debug output from several incorrect configurations.
SSH From an SSH Client Not Compiled with Data Encryption Standard (DES)
Solaris Debug
Router Debug
Bad Password
Router Debug
SSH Client Sends Unsupported (Blowfish) Cipher
Router Debug
Geting the '%SSH-3-PRIVATEKEY: Unable to retrieve RSA private key for' Error
If you receive this error message, it may be caused due to any change in the domain name or host name. In order to resolve this, try these workarounds.
Zeroize the RSA keys and re-generate the keys.
If the previous workaround does not work, try these steps:
Zeroize all RSA keys.
Reload the device.
Create new labeled keys for SSH.
Cisco bug ID CSCsa83601 (registered customers only) has been filed to address this behaviour.
Cisco Crypto Key Generate Rsa Modulus
Troubleshooting Tips
Cisco Switch Generate Ssh Keys
If your SSH configuration commands are rejected as illegal commands, you have not successfully generated a RSA key pair for your router. Make sure you have specified a host name and domain. Then use the crypto key generate rsa command to generate an RSA key pair and enable the SSH server.
When you configure the RSA key pair, you might encounter these error messages:
No hostname specified
You must configure a host name for the router using the hostname global configuration command.
No domain specified
You must configure a host domain for the router using the ip domain-name global configuration command.
The number of allowable SSH connections is limited to the maximum number of vtys configured for the router. Each SSH connection uses a vty resource.
SSH uses either local security or the security protocol that is configured through AAA on your router for user authentication. When you configure AAA, you must ensure that the console is not running under AAA by applying a keyword in the global configuration mode to disable AAA on the console.
No SSH server connections running.
This output suggests that the SSH server is disabled or not enabled properly. If you have already configured SSH, it is recommended that you reconfigure the SSH server in the device. Complete these steps in order to reconfigure SSH server on the device.
Delete the RSA key pair. After the RSA key pair is deleted, the SSH server is automatically disabled.
Windows 8.1 core product key generator. Note: It is important to generate a key-pair with at least 768 as bit size when you enable SSH v2.
Caution: This command cannot be undone after you save your configuration, and after RSA keys have been deleted, you cannot use certificates or the CA or participate in certificate exchanges with other IP Security (IPSec) peers unless you reconfigure CA interoperability by regenerating RSA keys, getting the CA's certificate, and requesting your own certificate again.Refer to crypto key zeroize rsa - Cisco IOS Security Command Reference, Release 12.3 for more information on this command.
Reconfigure the hostname and domain name of the device.
Generate an RSA key pair for your router, which automatically enables SSH.
Refer to crypto key generate rsa - Cisco IOS Security Command Reference, Release 12.3 for more information on the usage of this command.
Note: You can receive the SSH2 0: Unexpected mesg type received error message due to a packet received that is not understandable by the router. Increase the key length while you generate rsa keys for ssh in order to resolve this issue.
Configure SSH server. In order to enable and configure a Cisco router/switch for SSH server, you can configure SSH parameters. If you do not configure SSH parameters, the default values are used.
ip ssh {[timeout seconds] [authentication-retries integer]}Refer to ip ssh - Cisco IOS Security Command Reference, Release 12.3 for more information on the usage of this command.