Generate Ssh Key Pair Mac Os
You generate an SSH key through Mac OS X by using the Terminal application. Once you upload a valid public SSH key, Gerrit can authenticate you based on this key. An SSH key consists of a pair of files. One is the private key, which you should never give to anyone. Creating an SSH key on Windows 1. Check for existing SSH keys. You should check for existing SSH keys on your local computer. You can use an existing SSH key with Bitbucket Server if you want, in which case you can go straight to either SSH user keys for personal use or SSH access keys for system use. Open a command prompt, and run. Setup SSH keys – macOS. The following outlines the process of setting up key-based SSH login on Mac OS X and Mac OS X Server. To set up key-based SSH, you must generate the keys the two computers will use to establish and validate the identity of each other. You can create keys directly from your account: Log in into your account as the master user or as an admin user. Click the Users button. Pick the user you want to create keys for and choose the Generate SSH Keys button from the drop-down menu. You can generate an SSH key pair directly in cPanel, or you can generate the keys yourself and just upload the public one in cPanel to use with your hosting account. When generating SSH keys yourself under Linux, you can use the ssh-keygen command. To do so follow these steps: Open up the Terminal.
You generate an SSH key through macOS by using the Terminal application. Once you upload a valid public SSH key, the Triton Compute Service uses SmartLogin to copy the public key to any new SmartMachine you provision.
Joyent recommends RSA keys because the node-manta CLI programs work with RSA keys both locally and with the ssh agent. DSA keys will work only if the private key is on the same system as the CLI, and not password-protected.
About Terminal
Terminal is the terminal emulator which provides a text-based command line interface to the Unix shell of macOS.
To open the macOS Terminal, follow these steps:
- In Finder, choose Utilities from the Applications folder.
- Find Terminal in the Utilities listw.
- Open Terminal.
The Terminal window opens with the commandline prompt displaying the name of your machine and your username.
Generating an SSH key
An SSH key consists of a pair of files. One is the private key, which should never be shared with anyone. The other is the public key. The other file is a public key which allows you to log into the containers and VMs you provision. When you generate the keys, you will use ssh-keygen to store the keys in a safe location so you can bypass the login prompt when connecting to your instances.
To generate SSH keys in macOS, follow these steps:
Enter the following command in the Terminal window.
This starts the key generation process. When you execute this command, the
ssh-keygenutility prompts you to indicate where to store the key.Press the ENTER key to accept the default location. The
ssh-keygenutility prompts you for a passphrase.- Type in a passphrase. You can also hit the ENTER key to accept the default (no passphrase). However, this is not recommended.
You will need to enter the passphrase a second time to continue.
After you confirm the passphrase, the system generates the key pair.
Your private key is saved to the id_rsa file in the .ssh directory and is used to verify the public key you use belongs to the same Triton Compute Service account.
| Never share your private key with anyone! |
|---|
Your public key is saved to the id_rsa.pub;file and is the key you upload to your Triton Compute Service account. You can save this key to the clipboard by running this:
Importing your SSH key
Now you must import the copied SSH key to the portal.
- After you copy the SSH key to the clipboard, return to your account page.
- Choose to Import Public Key and paste your SSH key into the Public Key field.
- In the Key Name field, provide a name for the key. Note: although providing a key name is optional, it is a best practice for ease of managing multiple SSH keys.
- Add the key. It will now appear in your table of keys under SSH.
Troubleshooting
You may see a password prompt like this:
This is because:
- You did not enter the correct passphrase.
- The private key on your Macintosh (
id_rsa) does not match the public key stored with your Triton Compute Service account. - The public key was not entered correctly in your Triton account.

What are my next steps?
Right in the portal, you can easily create Docker containers, infrastructure containers, and hardware virtual machines. Microsoft office 2010 product key generator keygen free.
In order to use the Terminal to create instances, set up triton and CloudAPI as well as the triton-docker commandline tool.
Log in with an SSH private key on Linux and macOS
This article demonstrates how to use a private key to log in to a Linux速server by using a private key with a Terminal session on macOS速. However,you can follow the same process to use a private key when using anyterminal software on Linux.
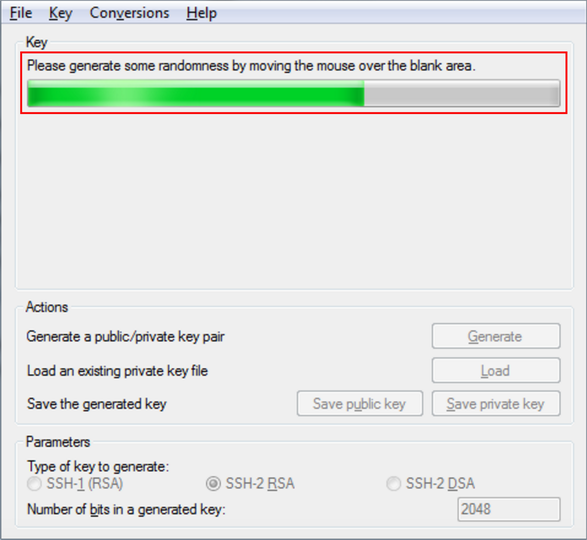
Note: For information about using Secure Shell (SSH) private keys on Microsoft速 Windows速 operating systems, see Logging in with an SSH Private Key on Windowsand Generate RSA keys with SSH by using PuTTYgen.
Prerequisites
To complete this process, you need the following software applications:
- SSH client software that is installed on your Linux or macOS operating system by default.
- Your favorite text editor. This example uses the vim text editor.
- Your private key. For more information about generating a key on Linux or macOS, see Connect to a server by using SSH on Linux or Mac OS X.
Log in with a private key
Using a text editor, create a file in which to store your private key. This example uses the file deployment_key.txt.
To edit the file in vim, type the following command:
After the editor starts, press i to turn on insert mode.
Paste your private key, such as the one in the following image, into the file.Be sure to include the BEGIN and END lines.
To save your changes, press Esc.
Type :wq to write the file and return to the command line.
Run the following command to change the file permissions to 600/risk-if-hsm-is-not-used-to-generate-encryption-key.html. to secure the key. You can also set them to 400.This step is required:
Use the key to log in to the SSH client as shown in the following example, which loads the key in file deployment_key.txt, and logs in as user demo to IP 192.237.248.66:
When you are prompted to confirm the connection, type yes and then press Enter.
If your SSH key requires a password, enter it when prompted to complete the connection.
Experience what Rackspace has to offer.
Mac Get Ssh Key
©2020 Rackspace US, Inc.
Generate Ssh Key Windows
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License